IT Security and Compliance Articles
Read articles from industry experts New Net Technologies to find out about best practices in keeping your IT systems secure.
- Category: File Integrity Monitoring
Lots of coverage this week relating to ‘Hand of Thief’, the latest black-market Trojan designed for any aspiring cyber-fraudster – yours for just $2000. It’s concerning news in that the threat to your personal data – predominantly your internet banking details – is an increasingly marketable commodity, but for the IT community, the additional interest in this particular piece of malware is that it has been engineered specifically for Linux.
- Category: File Integrity Monitoring
File Integrity Monitoring Software
Detect cyberattacks in their early stages with advanced file
and system integrity monitoring with NNT Change Tracker
The longer an attacker can lurk undetected in your IT environment, the more damage they can do. But today, organizations need an average of 287 days — nine and a half months! — to identify and contain a data breach.
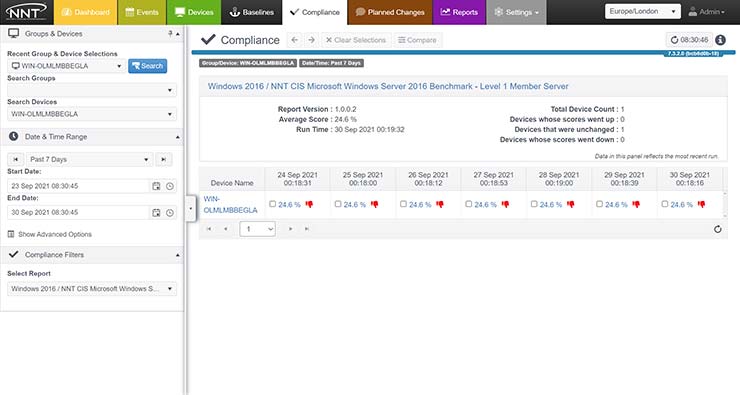
File integrity monitoring (FIM) solutions can help reduce the risk. Unlike traditional FIM solutions that focus on monitoring file activity, our file integrity monitoring solution is able to recognize known, expected and harmless file activity patterns, and detect and alert you on potentially dangerous and disruptive ones.
the NNT System and File Integrity Monitoring Tool
Spot true threat patterns promptly
Get notified about system changes that could be a sign of zero-day, malware or other cyberattack in progress.
Change Tracker monitors application files (e.g., DLLs), configuration files, registries, installed software, running processes, services and more.
Be confident that critical files are authentic
Quickly and accurately determine whether a change was part of planned maintenance, matches an approved change manifest or is whitelisted.
Reduce your compliance burden
Meet the requirements of PCI DSS, HIPAA, FISMA, CIS and other standards that recommend implementing FIM processes like monitoring changes to system and configuration files, performing critical file comparisons at least weekly, and more.
Harden your configuration management processes
Ensure that all IT systems remain securely configured at all times with at-a-glance visibility into event streams, planned changes, device activity and more.
Are you ready to get started in securing your IT environment with
industry-approved foundational controls, intelligent change control and automation?
- Category: COBIT-ITIL-ISO27001
With the growing awareness that cybersecurity is an urgent priority for any business, there is a ready market for automated, intelligent security defenses. The silver-bullet against malware and data theft is still being developed (promise!) but in the meantime, there are hordes of vendors out there that will sell you the next best thing.
- Category: File Integrity Monitoring
Why use FIM in the first place? For most people, the answer is ‘because my auditor/bank/security consultant said we had to!’ Security standards like the PCI DSS mandate a requirement for regular file integrity checks, including log file backups/archives, and this is the initial driver for most organizations to implement FIM.
- Category: PCI DSS Compliance
Using FIM, or file integrity monitoring has long been established as a keystone of information security best practices. Even so, there are still a number of common misunderstandings about why FIM is important and what it can deliver.
- Category: File Integrity Monitoring
No guns were used, no doors forced open, and no masks or disguises were used, but up to $500 Million has been stolen from businesses and individuals around the world. Reuters reported last week that one of the world's biggest ever cyber crime rings has just been shut down.
- Category: Change & Configuration Management
Is a gun better than a knife? I've been trying hard for an analogy, but this one kind of works. Which is better? A gun or a knife? Both will help defend you against an attacker. A gun may be better than a knife if you are under attack from a big group of attackers running at you, but without ammunition, you are left defenseless. The knife works without ammunition and always provides a consistent deterrent, so in some respects, gives better protection than a gun.
- Category: Device Hardening
Being the heart of any corporate application means your database technology must be implemented and configured for maximum security. Whilst the desire to ‘get the database as secure as possible’ appears to be a clear objective, what does ‘secure as possible’ mean? How hard is it to derive a suitable hardened build standard for your Oracle or SQL Server database?
- Category: PCI DSS Compliance
Simplest is still best - whether they are software-based (as in the so-called 'Dexter' or 'VSkimmer' Trojan - Google it for more information) or classic hardware interception devices, card skimming is still a highly effective means of stealing card data.
- Category: Device Hardening
Finding and interpreting the right hardening checklist for your Linux hosts can be a challenge. This guide gives you a concise checklist to work from, encompassing the highest priority hardening measures for a typical Linux server.
- Disable Windows Services
- What are the recommended Audit Policy settings for Windows & Linux
- Server Hardening Policy - Examples and Tips
- Server Hardening Checklist - Which Configuration Hardening Checklist Will Make My Server Most Secure?
- Windows Server 2008 2008R2 Hardening Guide
- File Integrity Monitoring Software
- Linux Server Hardening
- The Windows Advanced Audit Policy Configuration
- The Top Ten of Audit and Event Log Monitoring
- Which File Integrity Monitoring Technology Is Best For FIM? File Integrity Monitoring FIM or SIEM FIM?