There’s only one task harder than getting the right configurations for your IT systems, and that’s maintaining them. Even in the most well-run IT environment, the configuration settings of servers and other vital systems inevitably drift over time, which can compromise security and disrupt critical business processes.
Effective configuration management is a non-trivial task — unless you have the right tool. With Netwrix Change Tracker, you can quickly establish configurations based on industry benchmarks and then monitor them for any drift from your known-good baseline.
Harden configurations faster
Netwrix Change Tracker reduces the effort and guesswork involved in establishing safe configurations for critical systems by providing customizable build templates from respected standards bodies, including CIS, DISA STIG and SCAP/OVAL.

Get alerted to configuration drift
Netwrix Change Tracker alerts you to unauthorized configuration changes across your entire infrastructure so you can detect configuration drift as it happens and remediate it before it causes any damage.

Close the loop on change control
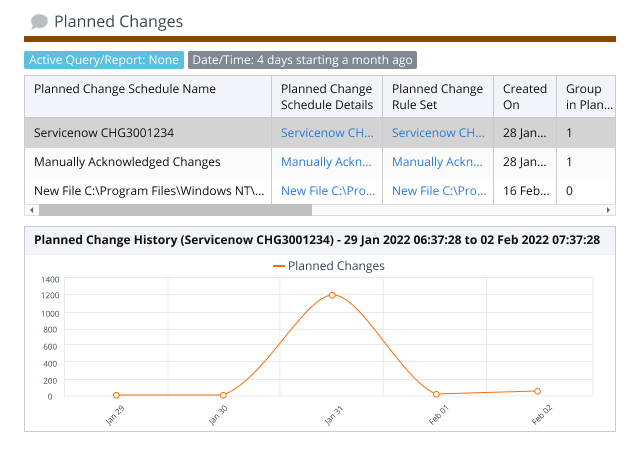
Netwrix Change Tracker removes the noise of authorized changes and empowers operations teams to focus on risky activity by coordinating with your IT service management (ITSM) solution.
Ensure regulatory compliance
Use pre-built reports to identify and remediate gaps in your configurations and help ensure your system setting are in compliance with industry regulations.

Rest easy with comprehensive coverage
Netwrix Change Tracker covers all of the following:
- Application and platform config file content
- Windows Group Policy, security and audit policy settings
- User accounts
- Installed software and updates
- Password policy
- Network-accessible open ports
- Files and file system structure, including ACL settings, group/owner, and secure hash value
- Windows registry keys and values
- Service startup and running states, and running processes
- Command outputs
- Database security settings and structure
- Public and private cloud system configuration settings