Netwrix Event
Log Manager
Richard Muniz,
Network/Systems Administrator
How Much Time Do You Spend on Reviewing Windows Server Event Logs Looking for Critical Events?
Stay on Top of Windows Server Logs
Event Viewer from Microsoft enables you to view and manage Windows event logs on your computer, gather information about hardware and software, and monitor Windows security events. However, sometimes the capabilities of this native tool are just not enough. For instance, you need to spend valuable time scrolling through tons of Windows server log files to spot critical events, such as the installation of a new program on a computer in your network or the creation of a new member in your Domain Admins group. But what if those events slip under your radar? Plus, Event Viewer only shows logs on the computer where it’s installed, so you can view events on only one machine in your network at a time, which is highly inconvenient.
Surpass Native Tools with Efficient Management of Windows Server Event Logs
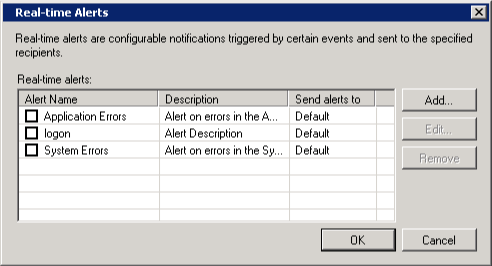
With Netwrix Event Log Manager, you can efficiently stay on top of Windows server logs across all computers in your network remotely, from a single desktop or laptop. Simply use an intuitive dialog box to specify which machines you need to collect logs from, the file system where the logs will be centrally stored, and the events you want to be alerted about. Then you will be notified in real time via email whenever a critical event occurs on any of those Windows servers, ensuring that no unauthorized activity goes unnoticed. Plus, you can prove to auditors that your logs are being properly archived.

Bill Kindle
Spiceworks Community
System Requirements
- Windows XP SP3 or above
- .NET Framework 2.0, 3.0 or 3.5
- 512MB of RAM
- 50MB of free disk space
