As Change Tracker users you’ll be familiar with the automated process used for on-boarding devices. Namely, when a new device registers, it is placed into a grouping structure based on the detected operating system.
For example, the below screenshot shows a Window server which has been assigned to the Windows 2012 R2 group and has therefore acquired the ‘CIS Win 2012R2 Member Server Base’ monitoring template.

The ‘CIS Win 2012R2 Member Server Base’ template contains monitoring for all key configuration elements contributing to the security of a Windows 2012 R2 system. For example, from a file integrity monitoring standpoint, the below coverage is applied:

In addition to the monitoring template, membership of the Windows 2012 R2 group means the system will also be assessed against the 2012 R2 Center for Internet Security (CIS) hardening baseline. The resulting report providing a score and detailed guidance on the most secure system configuration for a Windows 2012 R2 system.


This represents an excellent starting point and ensures that as soon as registration is complete, the system is protected under Change Tracker’s real-time monitoring of system integrity.
The configuration process, however, does not stop there! You will have built servers to support your business and whether they are database, file, or print servers, it is likely monitoring will need to be extended and coverage of all functional-specific areas added.
In this tip, we are going to look at the steps to extend the default monitoring and as with most things, this is best explained via an example! Our system, GEN7-DEMO-IP77 is a demo machine for Change Tracker Generation 7 and as such, is configured as a web server running Microsoft Internet Information Services (IIS). The addition of the IIS feature creates a number of functional items specific to IIS which will require monitoring. Within Change Tracker any extension to the monitoring is handled simply by creating a Change Tracker group and template set and, if available, uploading any available Change Tracker compliance report for the desired function.
Let’s look at the creation of each of these extensions individually.
NNT Change Tracker Compliance Report
NNT is a certified vendor to CIS and as such absorbs most CIS hardening guides into NNT Change Tracker. I have the IIS CIS report, entitled ‘NNT CIS Microsoft IIS 8 Benchmark Level 1 V1.4.0’ and so I can upload this to Change Tracker from Settings > Compliance Reports Templates > Upload template(s). We’ll come back the IIS reports later!

NNT Change Tracker Configuration Template
The configuration of the template is handled within Settings > Configuration Template. All I’ll need to do is click the ‘Add a Template’ button and create a name for my IIS monitoring template. In this example I am going to use the same naming convention as the compliance report template, ‘CIS Microsoft IIS 8 Benchmark Level 1 V1.4.0’. Once I’ve pressed ‘Update’ on the add template screen, a blank template is created. The next step is to find the template in the template list and click the ‘Edit’ button to begin configuration.

The ‘FIM File Integrity’ tab allows us to add the directories and files which are important. IIS creates a specific directory path where all web application files and folder are located. This path can be added into the template along with the hash function and the monitoring style of live tracking (Tracking) or a scheduled poll (Polling).
 4
4
Change Tracker monitors files by identifying files by their extension and has a number of out-of-the-box file types ready to go. Any file extensions required for our monitoring that fall outside of the Change Tracker default offerings can be added using the ‘Add a Custom Pathmatch Definition’. The below examples uses a wildcard extension which allows Change Tracker to monitor configuration files more relevant to web applications such as .php, .asp, .aspx, .config, .ascx and .asmx.


There are a number of other tabs within the template which cover additional monitoring, such as registry keys/values, command output, file contents etc. but for this example, I’ll save the template and move on.
NNT Change Tracker Group
With the report added and the template created and configured, I’ll next create a Change Tracker group for IIS: Click Settings > Groups, and hit the ‘Add’ button at the top of the group tree.
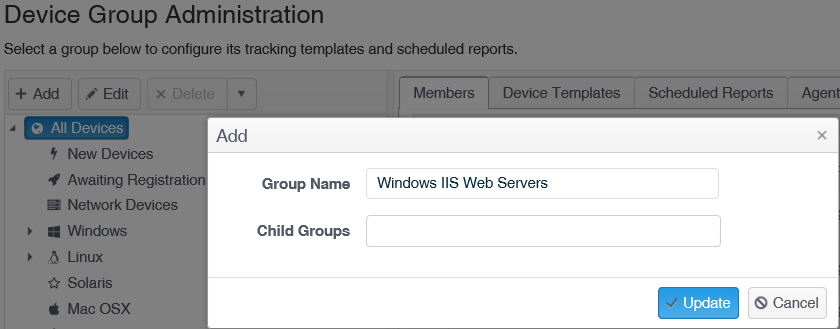
Once I’ve pressed the ‘Update’ button, the new group will appear in the group tree. I’ll highlight the new group and on the ‘Device Templates’ tab add our created configuration template, then move to ‘Scheduled Reports’ tab and add the IIS compliance report, creating a report schedule as I go.


With the creation of the NNT IIS Template and Group and the upload of the IIS compliance report, I am now ready to extend the monitoring for GEN7-DEMO-IP77. To apply the monitoring all I need to do is move to Settings > Agents & Devices, find GEN7-DEMO-IP77 in my device list and add the system to the ‘Windows IIS Web Servers’ group.

And that is all there is to it! If I check the green Device Tile for the GEN7-DEMO-IP77 I can see the addition of the IIS template to the system.

The new monitored path within the file integrity tab.

And finally the results of the compliance report.

As always, I hope this has proved to be useful and if you have any further question, please contact [email protected].










