See which NERC CIP compliance requirements you can address with Netwrix
The North American Electric Reliability Corporation (NERC) is a trans-national regulatory authority that ensures the reliability of the bulk electric power system in North America by developing and enforcing NERC reliability compliance standards for planning and operating the bulk electric system and minimizing the risk of system disturbances. NERC standards, which are designed to ensure the security of the IT infrastructure that supports North America's bulk electric system, are called NERC Critical Infrastructure Protection (CIP) standards.
To meet NERC CIP regulatory standards, organizations working in the energy and utilities industry have to enforce security controls, including both physical and cybersecurity controls, to protect their critical cyber assets and data. Some of the requirements cover policy creation and employee training, which are often outside of the scope of compliance management software. Therefore, when evaluating NERC CIP compliance tools, base your decision on the state of your IT environment and your cybersecurity priorities. NERC CIP compliance software from Netwrix supports the following cybersecurity controls:
To meet NERC CIP regulatory standards, organizations working in the energy and utilities industry have to enforce security controls, including both physical and cybersecurity controls, to protect their critical cyber assets and data. Some of the requirements cover policy creation and employee training, which are often outside of the scope of compliance management software. Therefore, when evaluating NERC CIP compliance tools, base your decision on the state of your IT environment and your cybersecurity priorities. NERC CIP compliance software from Netwrix supports the following cybersecurity controls:
CIP-004-6 — Cyber Security – Personnel & Training:
- R3 (3.1; 3.2), R4 (4.3; 4.4), R5 (5.1 – 5.5)
CIP-007-6 — Cyber Security – Systems Security Management:
- R4 (4.1-4.4), R5 (5.1; 5.4-5.7)
CIP-008-5 — Cyber Security — Incident Reporting and Response Planning:
- R2 (2.2; 2.3)
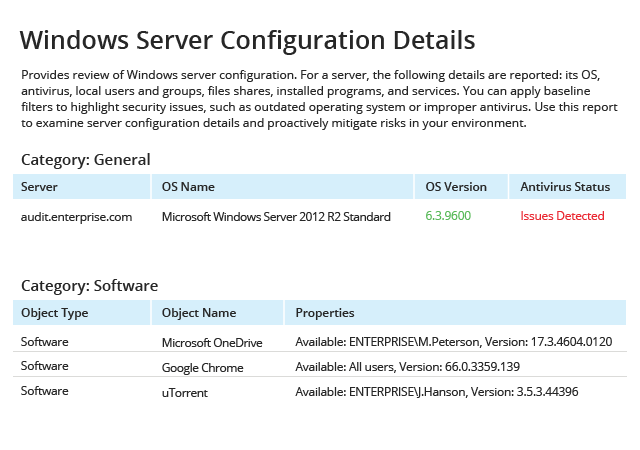
CIP-010-2 — Cyber Security — Configuration Change Management and Vulnerability Assessments:
- R1 (1.1; 1.2), R2 (2.1)
CIP-011-2 — Cyber Security — Information Protection:
- R1 (1.1; 1.2)
Learn more about how Netwrix can help you meet NERC CIP requirements and prove NERC compliance.
Depending on the configuration of your IT systems, your internal procedures, the nature of your business and other factors, Netwrix might also facilitate implementation of NERC CIP provisions and practices not listed above.
Find out how Netwrix can help you prove the NERC CIP compliance of your enterprise
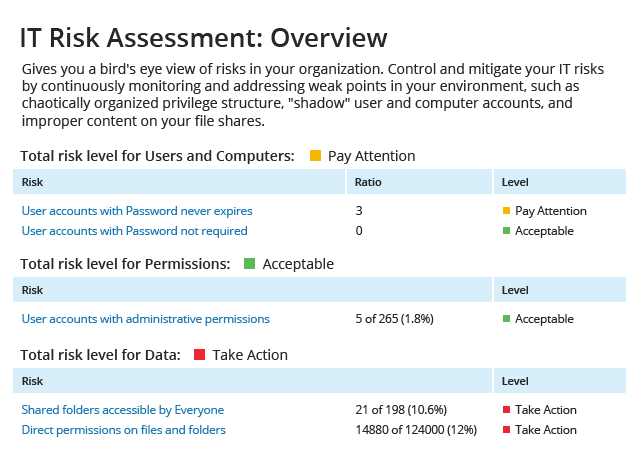
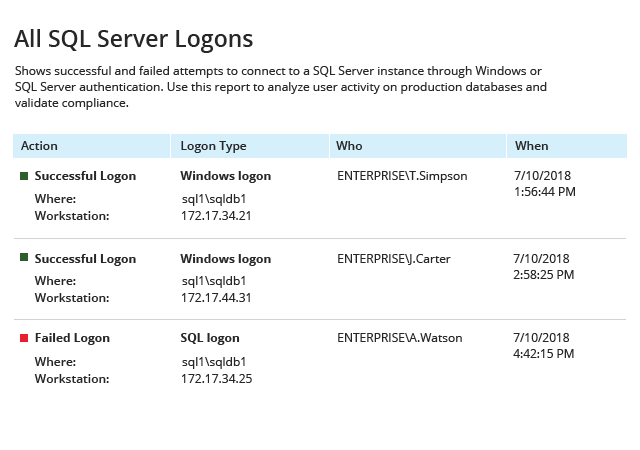
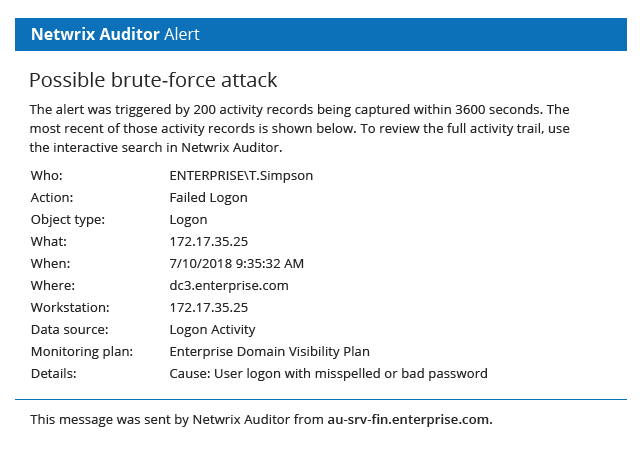
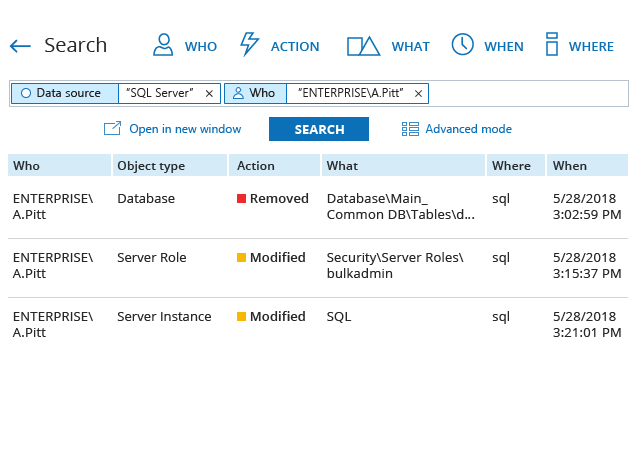
Netwrix provides visibility into changes, configurations and access events in on-premises and cloud-based systems. This NERC compliance software delivers security intelligence about security gaps in your environment, detects anomalies in user behavior, alerts you to threat patterns and makes it easier to investigate possible threats before they turn into security breaches. With API-enabled integrations, you can easily centralize automated security monitoring and reporting by feeding data from other on-premises and cloud-based applications and services into Netwrix. You can take advantage of free add-ons available for many well-known solutions, including ServiceNow ITSM, Cisco network devices and Amazon web services, as well as integrate applications and products built by your company.